News
Latest News

T-Mobile completes purchase of Mint and Ultra — what it means for subscribers
By Don Reisinger published
T-Mobile now owns Mint Mobile, but that doesn't mean things are changing right away.
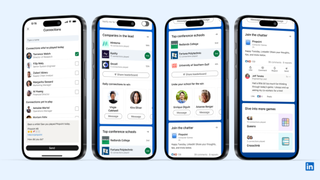
Wordle alternatives — LinkedIn launches 3 new puzzle games
By Scott Younker published
LinkedIn has created a gaming hub with three puzzle games to engage users on the career-focused social media network.

Apple Memorial Day sales 2024 — 21 early deals you don't have to wait for
By Morgan Bulman last updated
We're taking stock of all the early Apple Memorial Day sales popping up at Amazon, Best Buy and other retailers

Samsung Galaxy Watch Ultra now looks like a lock for this year — here’s why
By John Velasco published
The Galaxy Watch Ultra could be the premium model Samsung's expected to launch soon to complement its Galaxy Watch 7 series of smartwatches.

Bright red iPhone 15 refresh teased — what we know
By Scott Younker published
The organization behind the (PRODUCT)Red movement teased a potential new iPhone 15 in red.

Google Pixel 8a rumored release date, price and specs
By Philip Michaels last updated
The Google Pixel 8a should be the next Google phone to make its debut. Here's what we know so far about the Pixel 8a based on rumors and leaks.

'Andor' season 2: Everything we know so far
By Josh Bell published
The second and final season of Star Wars series "Andor" is on the way. Here's everything you need to know.

Dangerous new Wpeeper Android malware adds a backdoor to your phone to steal your data — how to stay safe
By Anthony Spadafora published
The Wpeeper malware may be new, but it already packs a punch and can steal all sorts of sensitive data from infected Android phones.

Your Instagram video feed is going to be better soon — here's how
By Scott Younker published
Instagram is updating its system to try and downplay the influence of content thieves and aggregators.

Borussia Dortmund vs PSG live stream: How to watch Champions League semi-final online and on TV today, team news
By Andy Murray last updated
The Borussia Dortmund vs PSG live stream in the Champions League semi-final sees both sides going all out to register a first-leg lead. Here's how to watch from anywhere.
Sign up to get the BEST of Tom’s Guide direct to your inbox.
Upgrade your life with a daily dose of the biggest tech news, lifestyle hacks and our curated analysis. Be the first to know about cutting-edge gadgets and the hottest deals.
