Antivirus
Latest about Antivirus

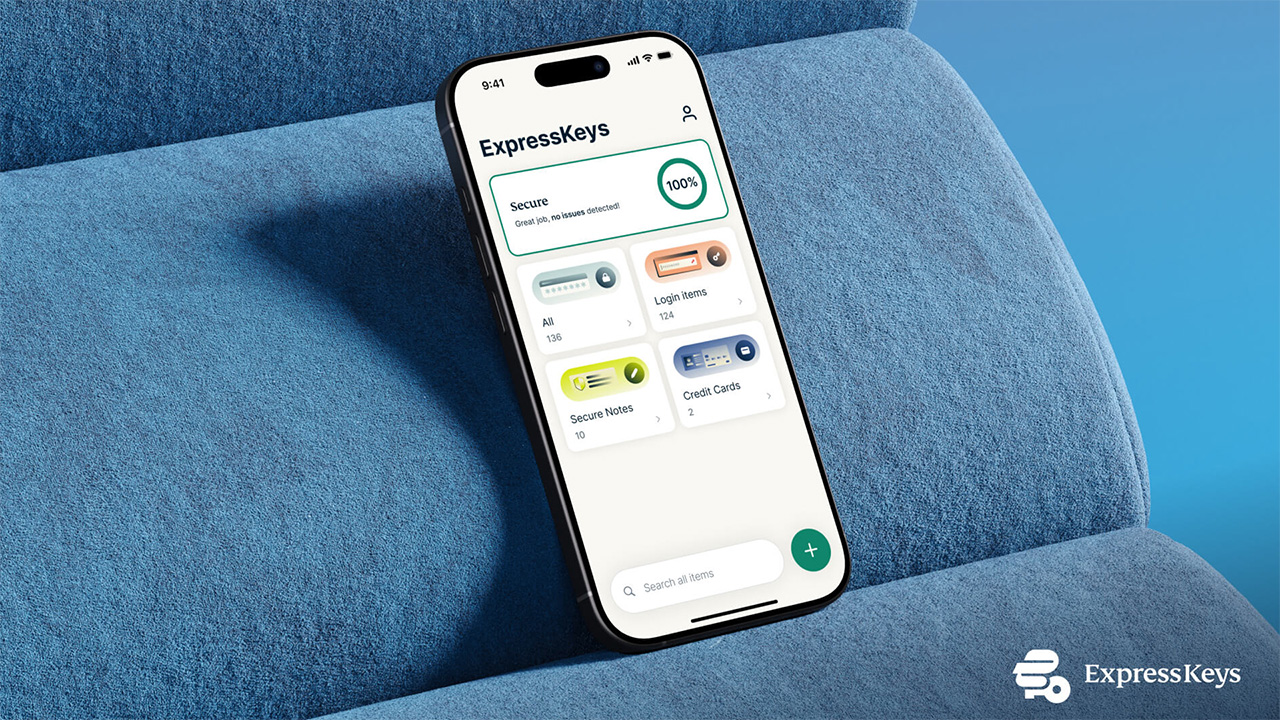
The best Android antivirus apps in 2026
By Amber Bouman last updated
The best Android antivirus apps can protect you from malware but also offer features like a VPN, password manager, phishing protection and more.

Webroot is knocking 50% off its Essentials plan — here's how to get yours
By Louis Ramirez published
Sponsored
Whether you're an avid shopper or gamer, Webroot Essentials can keep your devices secure from online threats. For a limited time, you can get 50% off its one-year plan.

Webroot is knocking 50% off its Total Protection plan — here's how to get it
By Louis Ramirez published
Sponsored
Webroot Total Protection offers everything you need to stay secure online. For a limited time, you can save 50% on your first year and pay just $89.99.

The best internet security suites for total online protection
By Anthony Spadafora last updated
The best internet security suites stop malware, manage your passwords, secure your connections and protect you from identity theft.

We've tested the best antivirus software to protect your computer and these are the 6 we recommend
By Anthony Spadafora last updated
Protect your computer and smartphone right now without breaking the bank — one of the best antivirus apps is even free!

Hurry! Norton is knocking up to 60% off its antivirus app
By Louis Ramirez published
Tom's Guide Approved - Sponsored Offer Norton
Norton makes one of the best antivirus apps we've tested. Right now you can save up to 60% off while protecting 5 of your devices. Here's how to get it.

The best Mac antivirus software in 2026
By Amber Bouman last updated
The best Mac antivirus software can help keep your MacBook, Mac mini, iMac and other Apple machines virus free.

Norton is slashing up to 60% off its antivirus app — here's how to get it
By Louis Ramirez published
Tom's Guide Approved - Sponsored Offer Norton
When it comes to antivirus apps, Norton makes some of the best that we've tested. Right now you can save up to 60% off. Here's how to get it.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!

 Club Benefits
Club Benefits