Apple Patches MacOS, iOS, Safari Against Spectre Attack
Apple on Monday issued a set of patches against the Spectre hardware security flaw for Macs, iOS devices and the Safari browser.
Apple patched Macs and iOS devices against the Intel-based Meltdown vulnerability last week, but iDevice users had to wait until today (Jan. 8) to receive patches for the even-more-complicated Spectre flaw.

The patches fix the Safari browser on OS X 10.11 El Capitan and macOS 10.12 Sierra, and macOS 10.13 High Sierra and iOS 11 overall. Spectre is generally pretty hard to exploit, but tests have shown that browsers are vulnerable to Spectre-based JavaScript attacks.
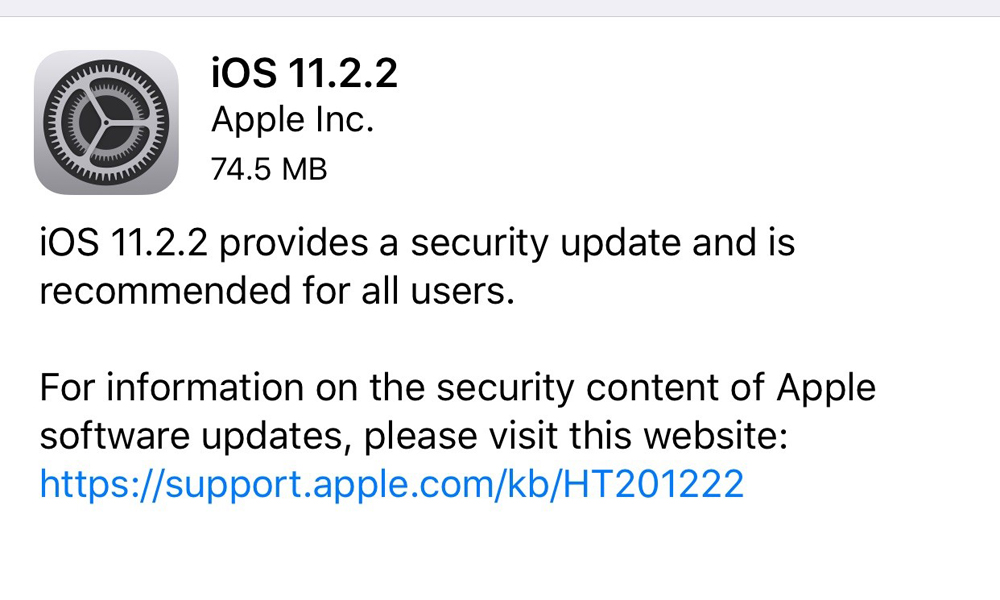
Apple users will in most cases receive notifications that the updates are ready. If not, go to the App Store on Macs and to Settings on iOS. To make sure that you're up to date, check to see if you've been updated to Safari 11.0.2 on Macs, or to iOS 11.2.2.
MORE: Meltdown and Spectre: How to Protect Your PC, Mac and Phone
The Meltdown-related flaw gives applications read access to the system's core memory, or kernel, which isn't supposed to happen. Using the Meltdown attack, a malicious program could read all data put into memory by the kernel or by any other application, and thus steal passwords, images, credit-card numbers and other kinds of sensitive information.
The flaw stems from the way Intel and Intel-related chips manage running memory. Intel sped up its chips beginning in 1995 by letting the kernel share some management features with applications. Nearly 23 years later, it turns out that was a bad idea.
Intel-based Macs (which is all Macs since 2006) are naturally affected, but surprisingly, so are iPhones and iPads. It turns out that Apple's 64-bit mobile chipsets, beginning with the A7 chip in 2013, share many similarities with Intel CPUs.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The Spectre-related flaws are even more complicated, but the Spectre attack essentially lets applications read each other's memory. Again, sensitive data could be compromised by malicious apps. In Spectre's case, malicious or corrupted websites could also steal date remotely from targeted machines.
Spectre affects all Intel and ARM-based chips, as well as some AMD ones. As almost all smartphones contain some ARM hardware, there was never any doubt that iPhones and iPads would be affected along with Macs.
Best Mac Antivirus Software

Kaspersky Internet Security for Mac's top-shelf malware detection and barely there system impact make it the best antivirus solution.

Avast Free Mac Security's malware-squashing proficiency, negligible performance impact and included password manager make it the best free option.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits












