Protecting yourself against ransomware

In our last piece, we took a look at the risks associated with public WiFi networks. Today, we’re going to start taking a deeper dive into some of the more dangerous threats on the web. We’ll start with ransomware.
If there’s one constant in the world of cybercrime, it’s that the majority of perpetrators prefer the path of least resistance. There are few things easier than holding data for ransom. Perhaps that’s why, since originating in 1989 with the AIDS Trojan, ransomware has proliferated across the web.
Ransomware is malicious software that operates on a deceptively simple concept. Every individual and organization has systems and data that are in some way important to them. Assets that are important enough that, were they locked out, the owners would be willing to pay to restore access.
- Read our guide to the best cloud storage services
- How to choose a cloud storage and backup provider
- What is Amazon S3?

With ransomware, there’s no need to find a marketplace for stolen information or go through the complexities of defrauding someone’s identity. All a criminal has to do is spam out the threat and wait for payment. Even worse, thanks to the emergence of Ransomware-as-a-Service, the bar for entry has never been lower.
These days, a criminal doesn’t even have to understand the ransomware they’re using. They can simply purchase the rights to a RaaS platform, aim it at their victims, and wait for the cash to start flowing - usually in the form of cryptocurrency such as bitcoin. As noted by Security Boulevard, many RaaS vendors even offer technical support to their criminal clients.

The good news is that with a bit of knowledge and preparation, ransomware is actually fairly easy to deal with.
First and most importantly, keep multiple, current backups of everything that’s important to you, and keep those backups isolated from your PC. The whole point of ransomware is to extort its victims by holding systems and data hostage. If you can simply roll back to a previous backup, the attack completely loses its power.
Second, make sure to always install security updates. The two most damaging ransomware attacks in recent memory - WannaCry and NotPetya - both targeted a vulnerability that had already been patched by Microsoft. As annoying as Windows Update can be, the alternative - running outdated software - is akin to painting a target on your back.

Third, be careful about downloading email attachments, opening files, or clicking links from people or websites you don’t know for certain are reputable. Phishing attacks - which we’ll discuss in greater depth in our next piece - are an extremely common delivery method for ransomware. Suffice it to say, a bit of mindfulness goes a long way in avoiding phishing attacks.
Finally, install the right security software. The award-winning Bitdefender, for instance, features multi-layer ransomware protection, protecting your documents, videos, pictures, and music against encryption by ransomware. This includes the ability to create automated, encrypted backups of your most important files and an Advanced Threat Defense module which can flag most malicious software before it even has a chance to infect.
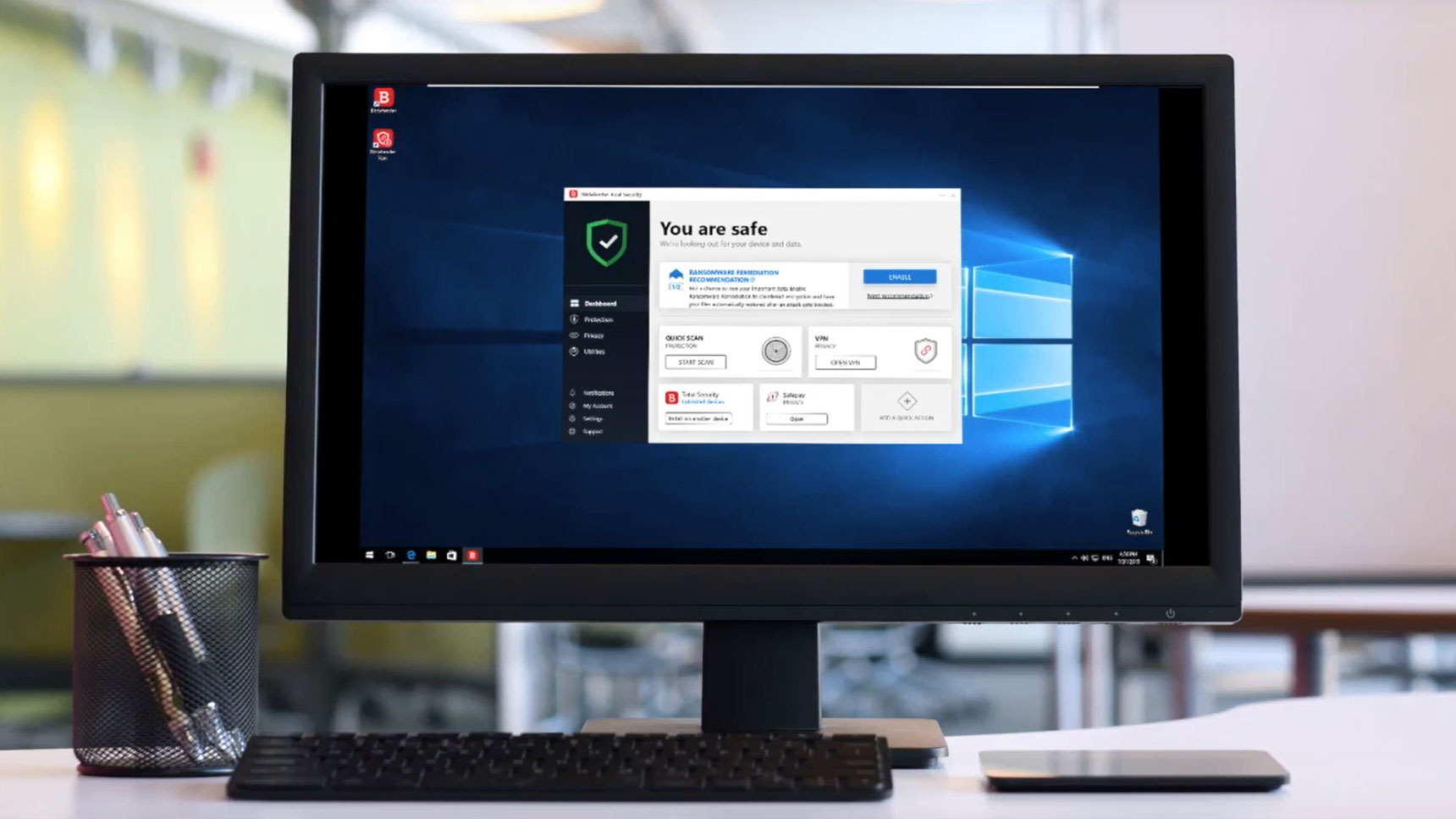
Better yet, with Bitdefender Family Pack, you can protect your entire household, safeguarding up to 15 devices against all manner of digital threats.
While Bitdefender provides excellent protection against all kinds of malicious software, it’s no replacement for mindfulness and conscientiousness. In that regard, it’s not enough to understand what ransomware is - you need to know how it’s delivered. Next time, we’ll discuss some red flags that’ll help you identify even the most complex phishing tactics.
- Cloud backup: the ultimate checklist to find the right provider
- Hybrid cloud storage: is it right for you?
- The changing market in cloud storage
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.

 Club Benefits
Club Benefits










