Cameras & Photography
Explore Cameras & Photography
Latest about Cameras & Photography

The best cameras in 2024
By Peter Wolinski last updated
Here are the best cameras for the money, including our favorite mirrorless cameras, DSLRs, point-and-shoot cameras and more.

Insta360 X4 review — the ultimate 360 camera
By Peter Wolinski published
Insta360 remedies the biggest weakness of 360 cameras to date

Best cheap cameras in 2024
By Richard Baguley last updated
The best cheap cameras offer good-enough image quality for a very low price.

Fujifilm Instax mini 99 review
By Jeanette D. Moses published
The Instax mini 99 is aesthetically pleasing, has a compact body and tons of advanced creative controls without losing sight of usability.
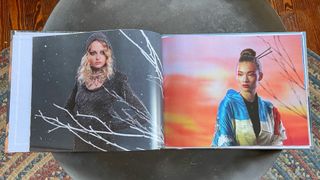
The best photo books in 2024: Mixbook, Shutterfly, Printique, Snapfish and more tested
By Dan Havlik last updated
What service should you use to make the best photo books and photo albums? We reviewed and compared five of the most popular services to find out.

The best digital photo frames in 2024
By Katie Mortram, Camilla Sharman last updated
Display your memories with the best digital photo frames in multiple sizes to suit every home and need.

Which Sony a6000 mirrorless camera is best for you?
By Mike Prospero last updated
Sony makes some of the best mirrorless cameras, but it can be hard to choose which model to get. Here are the best Sony mirrorless cameras for your needs (and budget).

Best mirrorless cameras in 2024
By Peter Wolinski last updated
The best mirrorless cameras for photographers of all types, experience levels, and budgets.
Sign up to get the BEST of Tom’s Guide direct to your inbox.
Upgrade your life with a daily dose of the biggest tech news, lifestyle hacks and our curated analysis. Be the first to know about cutting-edge gadgets and the hottest deals.


